Facebook has added support for USB key two-factor authentication to improve account security.
Here are the steps to enable USB key authentication on your Facebook account:
Step 1: Go to the Security settings page and expand the Logins Approval section.
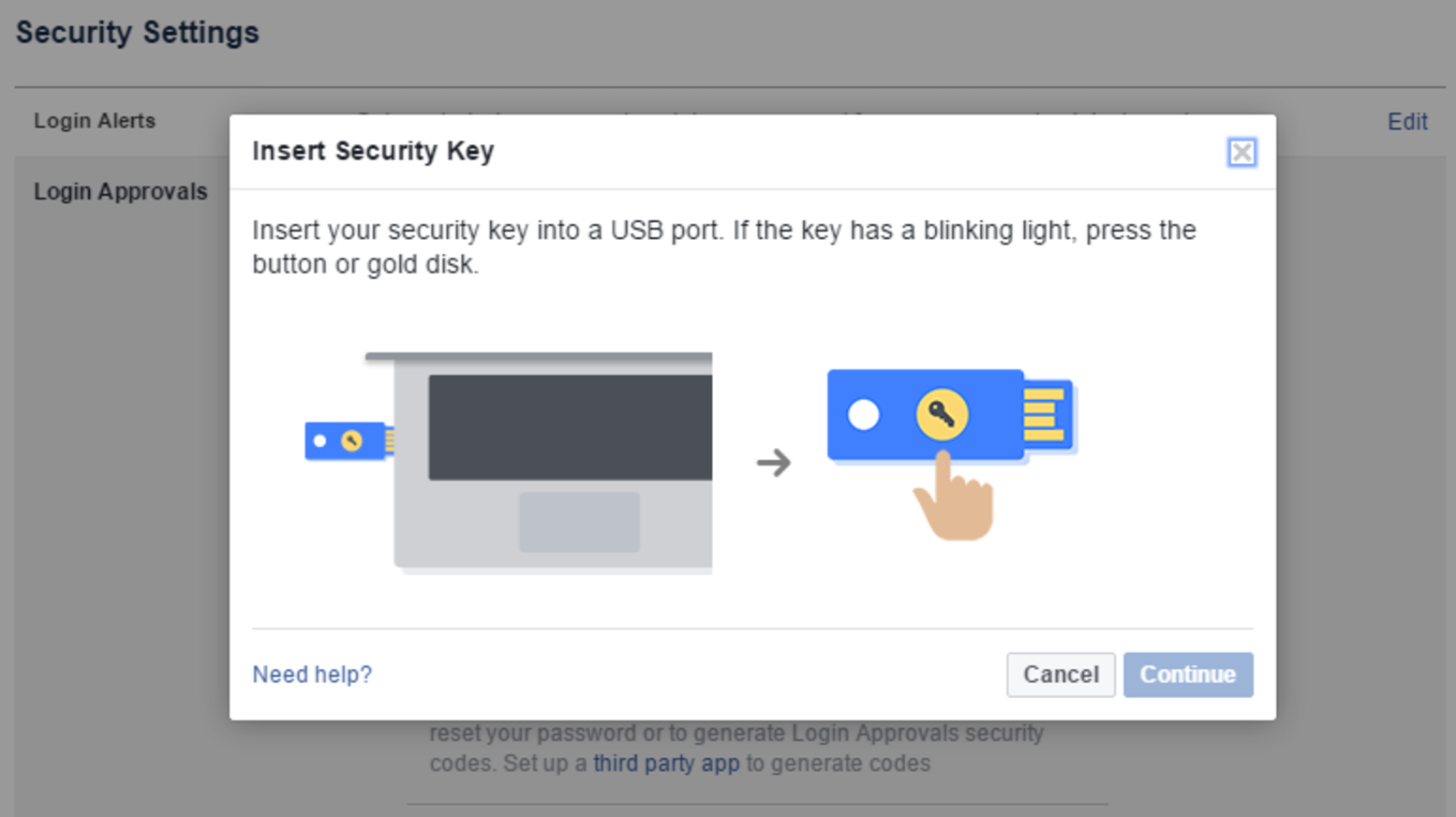
Step 2: In the Security Keys section, click the Add Key link and the Add Key button in the dialog that appears.
Step 3: When the prompt appears, plug in your USB key and tap its button when its light starts blinking.
Step 4: Once your key has been added, you’ll be prompted to re-enter your password to confirm the addition and to select a name to represent the physical key.
Step 5: When the process is completed, your newly added key will be visible under the Security Keys section.
If you’re not used to physical authentication keys, here are a few good practices:
Have backups keys: Just like everything else that fits in your pocket, keys can get lost (or possibly stolen). Therefore, you should have backup keys. Facebook’s security settings allow you to add multiple keys and to remove lost or broken ones.Have backup methods: For the moment, only the Facebook desktop website supports USB authentication, and the mobile website supports NFC-based keys such as the YubiKey Neo. Facebook’s mobile apps do not support physical keys yet. Therefore, you should still keep your app or SMS authentication enabled as a backup method.
Facebook’s USB authentication is not mandatory, but it is a welcomed move, as cybercriminals are targeting social media platforms at an accelerating pace. Hopefully, other social media services will follow suit and enable privacy-conscious users to breathe a sigh of relief.



Comments
Post a Comment