Beware! Your Credit/Debit Card Can Be Hacked In Just 6 Seconds
Card number, expiry date, CVV2, address -- everything is guessable
A new attack mechanism, called Distributed Guessing Attack, can steal your credit and debit card details in as few as six seconds. This assault exploits two basic security flaws in the online payment systems–unlimited guesses on payment pages and variation in the payment data fields.
Today, different kinds of cards have become the de facto means of online payments. This has also resulted in an increase in the number of online frauds taking place every month. The current situation, automatically, presents before us the question — what security methods are being taken to ensure a safe cashless transaction?
The researchers from the University of Newcastle have carried out a research and published their result in the IEEE Security & Privacy Journal. The study shows how an attack mechanism, called Distributed Guessing Attack, can bypass all the security measures deployed to ensure the safety of online transactions.
Surprisingly, this invasion can help the cyber criminals fetch your credit card numbers, security codes, expiry dates, and other information in as few as 6 seconds.
How Distributed Guessing Attack works?
The attack makes use of the reply (positive or negative) of web merchant’s payment page to guess the data. It exploits two weaknesses. First, the current payment systems don’t detect multiple invalid requests on the same card from different websites. It implies that unlimited guesses can be made by “distributing” the guesses over tons of websites. Second, as different merchants provide various fields for entering data, the attack scales well and the hacker can use the guessing attack to get information from one field at a time.
These two characteristics that look like a flaw, make things easy for the attackers to get all the credit card details. Within seconds, this attack can be launched on various payment pages. With the help of elimination, the correct card number, security code and CVV number can be verified.
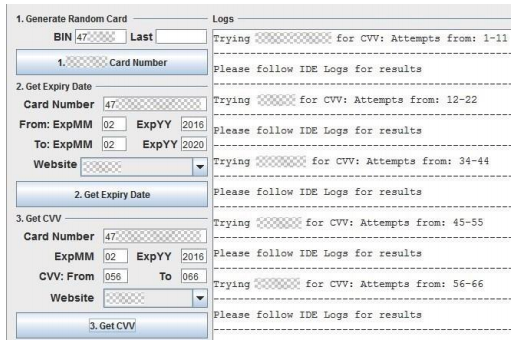 Screenshot of the website bot, farming CVV2 from multiple sites.
Screenshot of the website bot, farming CVV2 from multiple sites.
In the study, the attack was carried out using automated scripts written in Java Selenium browser automation framework. All the experiments were performed on Mozilla’s open source Firefox web browser.
After the study, the researchers have notified Visa and other affected sites. While some websites have hardened their security settings, many chose to ignore this warning.
In order to enhance the personal security, the researchers have suggested that the card-holders should use a single card for online payments and minimize the spending limit to as low as possible.
What do you suggest? Are our current cashless payment systems secure? Don’t forget to drop your views in the comments section belo
Comments
Post a Comment